Case Study: Low Level Memory
"HeartBleed" in Haskell
Modern languages are built on top of C
Implementation errors could open up vulnerabilities
"HeartBleed" in Haskell (1/3)
A String Truncation Function
import Data.ByteString.Char8 (pack, unpack)
import Data.ByteString.Unsafe (unsafeTake)
chop :: String -> Int -> String
chop s n = s'
where
b = pack s -- down to low-level
b' = unsafeTake n b -- grab n chars
s' = unpack b' -- up to high-level
"HeartBleed" in Haskell (2/3)
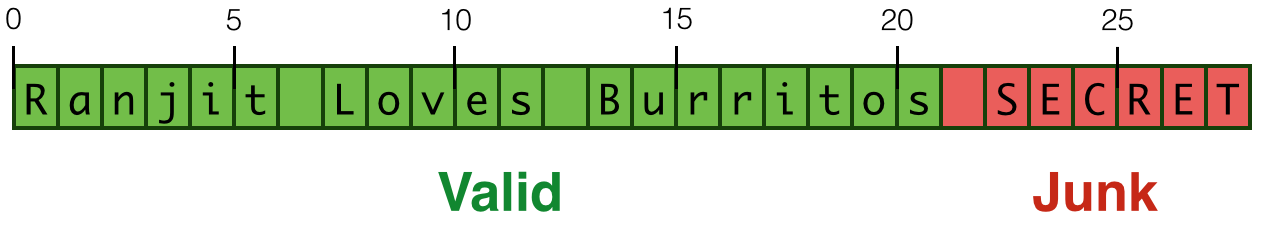
Works if you use the valid prefix size
λ> let ex = "Ranjit Loves Burritos"
λ> heartBleed ex 10
"Ranjit Lov"
"HeartBleed" in Haskell (3/3)
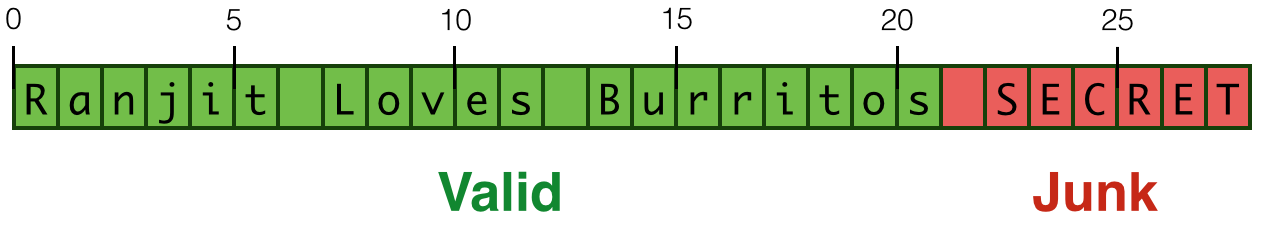
Leaks overflow buffer if invalid prefix size!
λ> let ex = "Ranjit Loves Burritos"
λ> heartBleed ex 30
"Ranjit Loves Burritos\NUL\201\&1j\DC3\SOH\NUL"
Types Against Overflows
Strategy: Specify and Verify Types for
- Low-level
PointerAPI - Lib-level
ByteStringAPI - User-level
ApplicationAPI
1. Low-level Pointer API
Strategy: Specify and Verify Types for
- Low-level
PointerAPI - Lib-level
ByteStringAPI - User-level
ApplicationAPI
Errors at each level are prevented by types at lower levels
1. Low-Level Pointer API
API: Types
Low-level Pointers
data Ptr a
Foreign Pointers
data ForeignPtr a
ForeignPtr wraps around Ptr; can be exported to/from C.
API: Operations (1/2)
Read
peek :: Ptr a -> IO a
Write
poke :: Ptr a -> a -> IO ()
plusPtr :: Ptr a -> Int -> Ptr b
API: Operations (2/2)
Create
malloc :: Int -> ForeignPtr a
Unwrap and Use
withForeignPtr :: ForeignPtr a -- pointer
-> (Ptr a -> IO b) -- action
-> IO b -- result
Example
Allocate a block and write 4 zeros into it
Example
Allocate a block and write 4 zeros into it
How to prevent overflows e.g. writing 5 or 50 zeros?
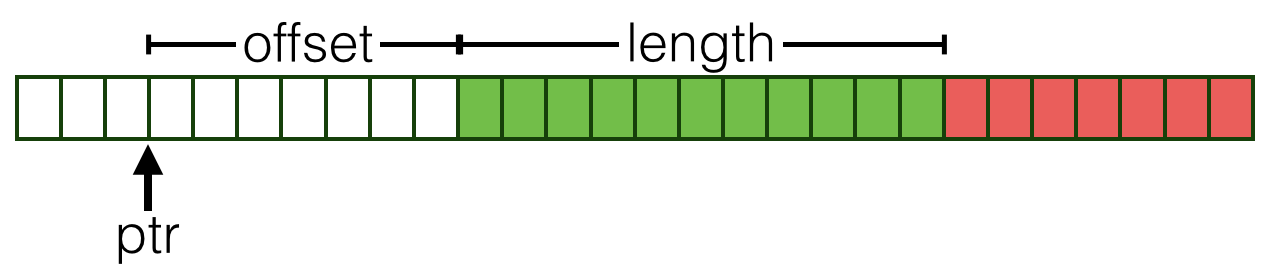
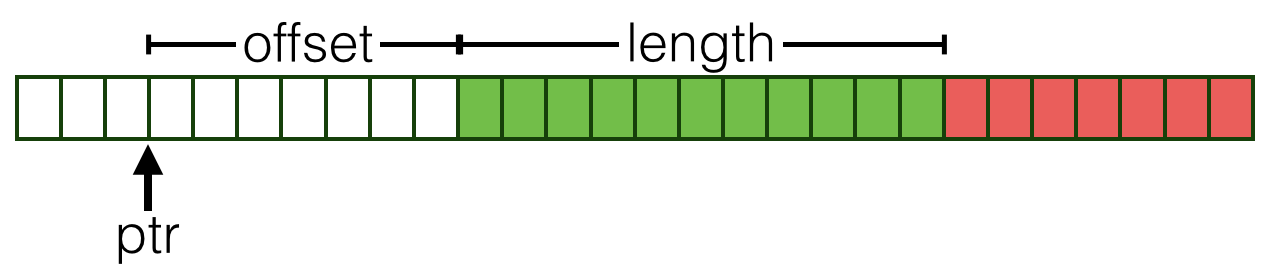
Step 1
Refine pointers with allocated size
Step 2
Track sizes in pointer operations
Refined API: Types
1. Refine pointers with allocated size
measure plen :: Ptr a -> Int
measure fplen :: ForeignPtr a -> Int
Abbreviations for pointers of size N
type PtrN a N = {v:_ | plen v = N}
type ForeignPtrN a N = {v:_ | fplen v = N}
Refined API: Ops (1/3)
Create
malloc :: n:Nat -> ForeignPtrN a n
Unwrap and Use
withForeignPtr :: fp:ForeignPtr a
-> (PtrN a (fplen fp) -> IO b)
-> IO b
Refined API: Ops (2/3)
Arithmetic
Refine type to track remaining buffer size
plusPtr :: p:Ptr a
-> o:{Nat|o <= plen p} -- in bounds
-> PtrN b (plen b - o) -- remainder
Refined API: Ops (3/3)
Read & Write require non-empty remaining buffer
Read
peek :: {v:Ptr a | 0 < plen v} -> IO a
Write
poke :: {v:Ptr a | 0 < plen v} -> a -> IO ()
Example: Overflow Prevented
How to prevent overflows e.g. writing 5 or 50 zeros?
2. ByteString API
Strategy: Specify and Verify Types for
- Low-level
PointerAPI - Lib-level
ByteStringAPI - User-level
ApplicationAPI
Errors at each level are prevented by types at lower levels
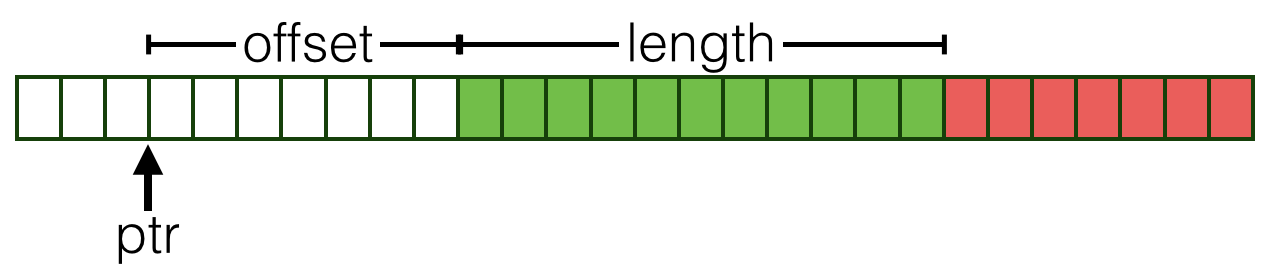
2. ByteString API
Type
Refined Type
Refined Type
A Useful Abbreviation
type ByteStringN N = {v:ByteString| bLen v = N}
Legal Bytestrings
Note: length of good2 is 3 which is less than allocated size 5
Illegal Bytestrings
Claimed length exceeds allocation ... rejected at compile time
API: create
Allocate and fill a ByteString
Implementation
API: pack
Specification
Implementation
API: unsafeTake
Extract prefix string of size n
Specification
Implementation
API: unpack
Specification
unpack
:: b:ByteString -> StringN (bLen b)
Implementation
unpack b = you . get . the . idea -- see source
3. Application API
Strategy: Specify and Verify Types for
- Low-level
PointerAPI - Lib-level
ByteStringAPI - User-level
ApplicationAPI
Errors at each level are prevented by types at lower levels
3. Application API
Revisit "HeartBleed"
Lets revisit our potentially "bleeding" chop
A Well Typed chop
{-@ chop :: s:String
-> n:{Nat | n <= len s}
-> {v:String | len v = n} @-}
chop s n = s'
where
b = pack s -- down to low-level
b' = unsafeTake n b -- grab n chars
s' = unpack b' -- up to high-level
END CUT -->
"HeartBleed" no more
"Bleeding" chop ex 30 rejected by compiler
Recap: Types vs Overflows
Strategy: Specify and Verify Types for
- Low-level
PointerAPI - Lib-level
ByteStringAPI - User-level
ApplicationAPI
Errors at each level are prevented by types at lower levels
Bonus Material
Nested ByteStrings
For a more in depth example, let's take a look at group, which transforms strings like
"foobaaar"
into lists of strings like
["f","oo", "b", "aaa", "r"].
The specification is that group should produce a list of ByteStrings
- that are all non-empty (safety)
- the sum of whose lengths is equal to the length of the input string (precision)
We use the type alias
to specify (safety) and introduce a new measure
to specify (precision). The full type-specification looks like this:
As you can probably tell, spanByte appears to be doing a lot of the work here, so let's take a closer look at it to see why the post-condition holds.
LiquidHaskell infers that 0 <= i <= l and therefore that all of the memory accesses are safe. Furthermore, due to the precise specifications given to unsafeTake and unsafeDrop, it is able to prove that spanByte has the type
where ByteStringPair b describes a pair of ByteStrings whose lengths sum to the length of b.